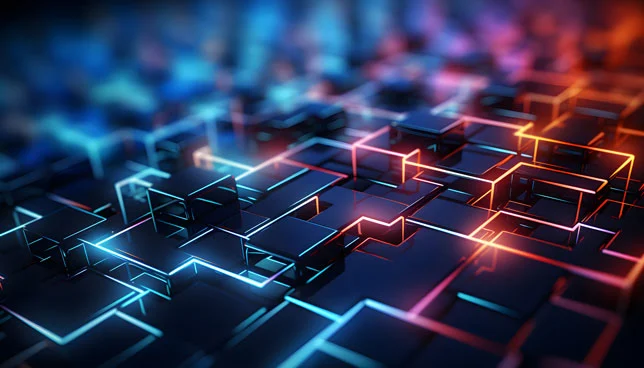
The core of this operation is the utilization of a Phishing-as-a-Service (PhaaS) toolkit known as "EvilToken." This platform has emerged as a primary driver for large-scale device code abuse, allowing threat actors to automate complex attack chains that were previously labor-intensive. By integrating generative AI into their workflows, attackers have successfully increased the success rates of their campaigns while simultaneously making them harder for automated detection systems to identify.
The Evolution of the Phishing Landscape
For decades, phishing attacks relied on the "spray and pray" method—sending millions of generic emails in the hope that a small percentage of recipients would click a malicious link and enter their credentials into a spoofed login page. However, as email filters have become more adept at identifying suspicious keywords and malicious URLs, threat actors have been forced to innovate.
The emergence of AI-driven campaigns marks a new era of precision. Instead of generic lures, attackers now use generative AI to craft highly personalized messages tailored to the specific professional roles of their targets. These emails often include contextually relevant documents, such as invoices, project briefs, or legal PDFs, which significantly increase the level of trust and engagement from the victim.
Furthermore, the research indicates a shift in the ultimate goal of these attacks. While password theft remains a concern, modern sophisticated actors are increasingly focused on "token theft." By obtaining a valid authentication token, an attacker can maintain access to a corporate environment without ever needing to know the user’s password, effectively bypassing many forms of Multi-Factor Authentication (MFA) that rely on simple push notifications or SMS codes.

The Anatomy of an AI-Driven Attack
The Microsoft research highlights a methodical, multi-stage process that distinguishes this campaign from less sophisticated operations. The attack chain is characterized by a high degree of automation and a deep understanding of corporate authentication workflows.
Phase 1: Reconnaissance and Active Filtering
The campaign begins long before the first phishing email is sent. Attackers conduct extensive reconnaissance to identify and filter active email accounts within a target organization. This process typically occurs 10 to 15 days prior to the actual attack. During this window, the threat actors use automated tools to verify which accounts are valid and which are most likely to yield high-value access, such as those belonging to executives, IT administrators, or finance teams.
Phase 2: AI-Generated Personalization
Once the targets are identified, generative AI is employed to create the lure. By analyzing the target’s industry, role, and potentially even their public social media or LinkedIn presence, the AI generates language that mimics professional correspondence. This removes the tell-tale signs of traditional phishing, such as poor grammar or awkward phrasing, making the emails nearly indistinguishable from legitimate internal communications.
Phase 3: Bypassing Security Filters via Cloud Redirects
To avoid being flagged by secure email gateways (SEGs), the attackers do not link directly to a malicious site. Instead, they pass their links through legitimate cloud services and reputable redirects. By utilizing the "reputational capital" of trusted domains like those hosted on major cloud providers, the attackers ensure their emails reach the victim’s inbox.
Phase 4: Device Code Flow Abuse
The most critical and technically sophisticated part of the attack involves the abuse of the Microsoft device code flow. Originally designed for devices that lack an easy input method (such as smart TVs or IoT devices), the device code flow allows a user to sign in on a secondary device by entering a code on a legitimate Microsoft login page.

When the victim clicks the phishing link, they are presented with a genuine Microsoft authentication page. The attacker’s system, acting in the background, triggers a device code generation request. The victim sees a real code and enters it into the real Microsoft portal. Because the portal is legitimate, the user feels safe. However, by entering that code, the victim unknowingly authorizes a session for the attacker.
Overcoming the 15-Minute Expiration Barrier
One of the primary challenges for attackers using device code abuse in the past was the 15-minute expiration window for generated codes. If a victim did not click the link and enter the code almost immediately, the attack would fail.
The EvilToken toolkit solves this through real-time automation. The researchers found that the threat actors triggered the code generation at the exact moment the user interacted with the phishing link. This "just-in-time" code generation ensures that the authentication flow remains valid throughout the user’s interaction, significantly improving the reliability and scalability of the attack.
Supporting Data and Technical Scale
The scale of this campaign is facilitated by the use of modern cloud infrastructure. According to the report, threat actors are leveraging serverless hosting and ephemeral systems to run their operations. By spinning up thousands of short-lived systems, they can execute massive campaigns and then dismantle the infrastructure before security teams can trace the origin of the attack.
Data from Microsoft Defender suggests that these AI-enabled campaigns have a significantly higher "click-to-compromise" ratio compared to traditional methods. While traditional phishing might see a success rate of less than 1%, the highly personalized and technically sound nature of device code abuse can yield much higher results, particularly when targeting non-technical staff in high-pressure roles like finance or human resources.

Post-Compromise Activity and Lateral Movement
Once the attacker secures an authentication token, the focus shifts to exploitation. Because the token grants access to the user’s full suite of cloud applications, the attacker can:
- Access Sensitive Communications: Read emails and Teams messages to gather internal intelligence.
- Map the Organization: Use the global address list to identify key decision-makers and financial controllers.
- Establish Persistence: Create new mail forwarding rules or register new devices to ensure continued access even if the initial token expires.
- Exfiltrate Data: Systematically download sensitive documents from SharePoint or OneDrive.
The researchers noted that the attackers are particularly interested in "living off the land," using the organization’s own tools and permissions to move laterally through the network without triggering traditional malware alarms.
Official Responses and Industry Implications
Microsoft has responded to these findings by urging organizations to move toward more robust identity security models. The company emphasized that security models built solely around passwords and basic detection are no longer sufficient in an era where AI can automate the bypass of these defenses.
"This activity aligns with a broader trend we are seeing where attackers are moving ‘upstream’ in the authentication process," a Microsoft security spokesperson stated. "By abusing legitimate protocols like device code flow, they are effectively turning our own security and convenience features against us."
Cybersecurity analysts suggest that this campaign should serve as a wake-up call for the industry. The fact that the attack uses legitimate login pages means that traditional "look at the URL" training for employees is becoming less effective.

Recommendations for Mitigation
To defend against AI-driven device code abuse, security researchers recommend a multi-layered approach:
- Restrict Device Code Flow: Organizations should disable the device code authentication flow if it is not strictly necessary for their operations. If it is required, it should be restricted to specific users or devices via Conditional Access policies.
- Continuous Access Evaluation (CAE): Implementing CAE allows identity providers to revoke tokens in real-time if a risk is detected, such as a login from an unusual location or a change in user state.
- Transition to Phishing-Resistant MFA: While standard MFA is better than nothing, it is susceptible to token theft. Moving toward FIDO2-based authentication or hardware security keys provides the highest level of protection against these types of attacks.
- Enhanced Monitoring: Security Operations Centers (SOCs) should monitor for unusual sign-in properties related to device code flows, particularly those originating from unexpected IP addresses or involving administrative accounts.
- User Awareness 2.0: Training programs must be updated to inform employees about the risks of device code requests. Employees should be taught that they should never enter a code into a website unless they have personally initiated a login on a device that explicitly requested it.
Conclusion
The discovery of the AI-driven EvilToken campaign underscores the escalating arms race between cybercriminals and defenders. As generative AI continues to lower the barrier to entry for sophisticated social engineering, and as automation allows for the exploitation of complex authentication flows at scale, the burden of defense shifts from the individual user to the architectural level of the organization.
The findings from the Microsoft Defender Security Research Team highlight a critical truth in modern cybersecurity: the most dangerous threats are no longer those that break into systems, but those that log in using valid, albeit stolen, credentials and tokens. Continuous monitoring, stricter identity controls, and a fundamental shift in how organizations perceive "trusted" authentication are now essential components of a modern security posture.







Leave a Reply